A Complete Guide to Protecting Modern Digital Infrastructure
The safe digital communication of the modern world is the key of network security. Every organization whether small or big that is operating requires a safe network as this is a requisite of that organization. The network infrastructure security has proved to be an area of concern owing to its increased and sophisticated cyber threats. Network security is not merely software i.e. antivirus programs or firewalls installed, it is the entire field of technology, policy, processes and human consciousness.
Network security is simply the art of keeping networks, computers and information out of the hands of unauthorized persons, abusers, damage or stealing. The result of not possessing proper network security may lead to loss of confidential information, breakage of a system as well as confidence. Later, the idea of network security, its principles, threats, technologies, strategies and trends are discussed in this paper.
________________________________________
Prerequisites of Network Security.
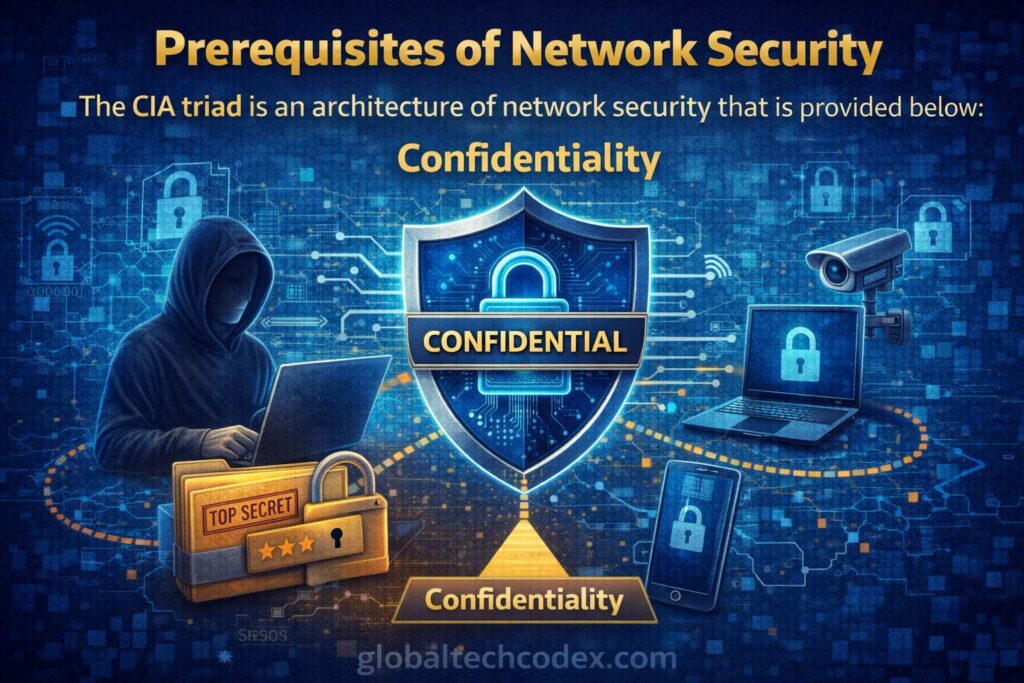
The CIA triad is an architecture of network security that is provided below:
Confidentiality
Confidentiality is a commitment that there is access to confidential information by the testified personnel. The encryption and access controls in addition to the authentication systems block the unauthorized viewing of the private information including the financial information or the personal information by the unauthorized users.
Integrity
Integrity ensures that the data is correct and none of the individuals is distorting it. Data integrity is achieved by using security measures such as hashing and digital signature.
Availability
The availability can be utilized in order to have data and system available when required. Redundancy, backups and denial-of-service attack are some of the measures that can be used to guarantee service continuity.
All decisions made in the network security design will be guided by the combination of these three principles.
________________________________________
Threats in Network Security.
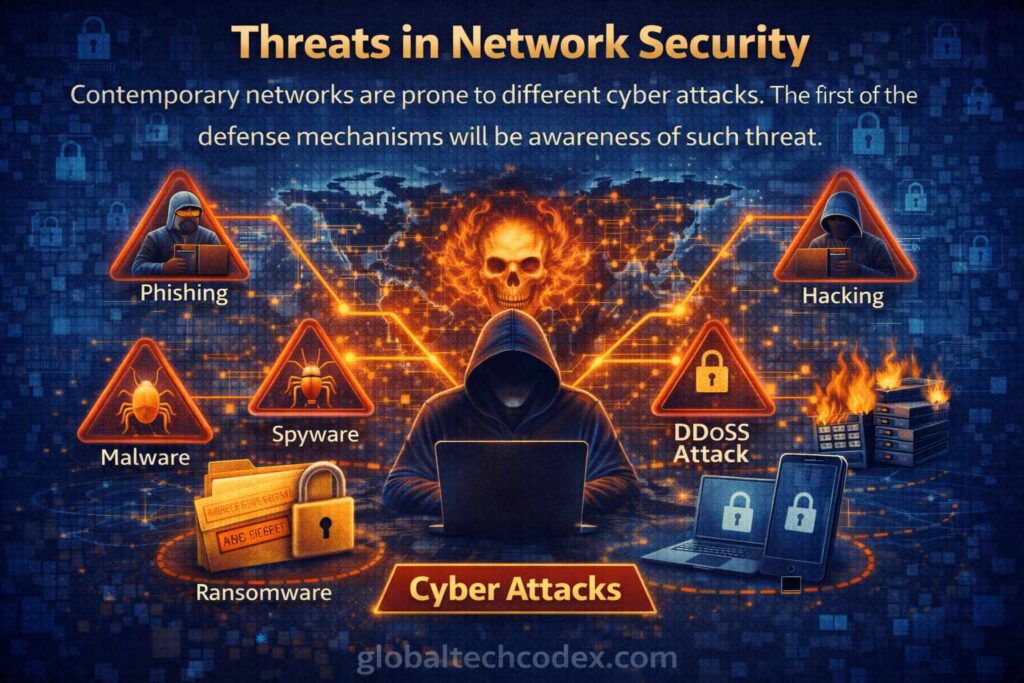
Contemporary networks are prone to different cyber attacks. The first of the defense mechanisms will be awareness of such threat.
Malware
Malware consists of virus, worms, trojans, spy programs that are used to destroy or steal data. Malware that is introduced may propagate through a network at an alarming rate and result in a vast amount of damage.
Ransomware
Ransomware is the type of malicious software that encodes files and claims to provide money to restore the files. It has turned out to be one of the most lucrative forms of cybercrime that include hospitals, businesses and governments.
Phishing Attacks
Phishing utilizes fraud email or web pages that are then used to deceive people into providing their password or financial data. This is a human trust based attack but not technical.
Distributed Denial-of-Service (DDoS).
The DDoS attacks flood the servers that are faulting the services to the known customers. Such attacks can bring even large institutions to their knees.
Insider Threats
Security breaches can be done accidentally by employees who are entitled to access the system and contractors. Insider threats are normally very hard to manage since they are internal.
________________________________________
The greatest Network Security Technologies.
The network security is on the multi-layers of the security.
Firewalls
Firewalls are applied to offer an access point between the inner and the outer networks which are trusted. They deter suspicious traffic by blocking the traffic according to the established set rules. The next-generation firewalls available in the modern world have the capability to scan encrypted traffic hence identifying elaborate threats.
Intrusion Detection and Prevention systems (IDPS).
IDPS system is used to monitor network traffic on behavior that is abnormal. It has detection systems that warn the administrators, and prevention systems that block the threats as they occur.
Encryption
The code is not made out but rather the ciphertext is sent. It is unlikely that even in the case when attackers intercept the encrypted information they are not able to understand this information without key. The proceeds of the SSL/TLS protocols and VPNs are used in the securing of the Web sites and remote connection respectively.
Virtual Private Networks (VPNs).
VPNs establish both secure paths between remote and corporate networks. They are necessary in such protection of the employees who work at home or go using the public Wi-Fi.
Access Control Systems
Customers are checked and restricted by authentication and authorization systems. Multi-factor authentication is an additional factor of security since the verification is on an added basis compared to passwords.
Network Segmentation and Architecture Network Segmentation and Architecture Network segments are subdivided into groups based on their nature.
Network segmentation also sub divides a network into small segments. Sensitive systems are not networked with common areas of users. When the hackers have broken into one part of a network, they cannot move freely in the whole network.
For example:
• The company systems are not connected to the guest Wi-Fi.
single financial databases Financials databases are not connected to employee devices.
• The systems of production and testing are isolated.
Segmentation minimizes destruction of attacks and better tracking.
________________________________________
Human Factor of Network Security.
Security does not just depend on technology. The human behaviour is rather important.
There is a high probability of the employees being victimized by phishing or bad passwords. Security awareness training is a training that informs the user to be in a position to be aware of the existence of threat and in addition, one has to be in a position to adhere to the best practices. Companies need to inculcate a culture in which cybersecurity is the bane of all.
Key practices include:
- Establishment of hard and special passwords.
- Obtaining protection against dubious email links.
- The software is modified periodically.
- Suspicious behavior reporting.
A highly educated work force is one of the highest order safeguards.
________________________________________
Incidents Response and monitoring.
No safe network exists. They ought to incorporate the element of constant monitoring whereby threats could be realized early enough.
Logging and analytics tools are tools that help security teams to monitor network activity. Incident response plan will make sure that incident containment and recovery is fast in case of incident.
A good response has:
1. Identifying the breach
2. Containing the threat
3. Eradication of evil aspects.
4. Reviving normal operations.
5. Analyzing lessons learned
______________________________________
Cloud Security Challenges
Network boundaries are not necessary because the organizations are moving to the cloud platform. Cloud security should secure the distributed systems and the remote access points.
Cloud vendors share equal liability with their customers. Infrastructure security is guaranteed by providers but it is the role of the organizations to restrict access, encryption and compliance.
Cloud environments require:
- Strong identity management
- Encrypted storage
- Secure APIs
- Regular audits
New vulnerabilities may arise due to the adoption of the cloud without proper planning.
________________________________________
Zero Trust Security Model
One of the recent network security practices is Zero Trust. Automatically, all the access requests are verified rather than being permitted to internal users.
The action principle is simple, i.e., do not trust and make sure.
Users in the network are also compelled to do continuous authentication. This type of model reduces the insider threat and eliminates the potential of attackers acting freely when they get inside.
Zero trust is also essential under remote workplace conditions whereby, there cease to exist network fences.
________________________________________
Law and Legal Compliance.
Many sectors are under obligation to subscribe to strict laws on cybersecurity. The law of protecting data is present in the fields of healthcare, finance, and government.
compliance enforce:
- Data protection standards
- Privacy safeguards
- Security audits
- Incident reporting
Failure to practice it can be severely fined and subjected to legal measures. Good network security is ensuring that it secures both the safety of operations and law protection.
________________________________________
The Artificial Intelligence in the Security.
The network security is evolving due to artificial intelligence. The capability of AI technologies to analyze trends in big amounts of data lets them detect threats faster than a human being.
AI-driven systems:
- Predict vulnerabilities
- Automates threat response
- Detect unusual behavior
- Adapt to evolving attacks
The cyber threats will transform into more complex attacks and this will require the use of intelligent automation.
________________________________________
A Future Network Security.

Flexibility will be the main focus of the network security future. The growth of the achieved attack surfaces is also accompanied by the growth of the number of IoT devices, remote work, and cloud computing.
Organizations must:
You must invest in skilled and well educated cybersecurity specialists just as you would.
• Defend against the attack at all times.
• The adoption of the best security systems.
Security is not a single activity and in fact, it is a long-lasting one.
________________________________________
Conclusion
The scope of network security is an extremely crucial field of knowledge because in the modern world it protects the digital backbone of the modern society. It is a combination of integrative approaches, which entail technology, strategy, and human mindfulness to safeguard information and secure trust. Layered defense, encryption, monitoring, segmentation and education are effective ways that an organization can mitigate cyber risk to a great extent.
Threats may continue to evolve yet the networks will be threats-resistant and dependable with dynamic security architecture planning and strength. Network security has ceased being a choice in the world that has become digitally interconnected but a survival and growth necessity.