In the present globalized world, we virtually do all our business online. We shop, work, watch the media, spend money, save personal data, communicate with friends and save data using the internet. Even though this online convenience has led to some ease in life, there are some grave issues that are posed on privacy, security and tracking of information.
Some of the cyber threats that have been increasing include hackers, identity theft, tracking behaviors of data and surveillance. Internet advertisers, internet service providers and a great number of other websites follow the activities of the user so that they can collect personal information. Security risk is also a security threat to users that use the general Wi-Fi networks that are usually used in cafes, airports, and hotels.
This is where Virtual Private Network (VPN) comes in as it is quite useful. A VPN is a protective barrier between your computer or phone and the internet which could enable you view it more safely and privately.
We will touch upon the process of VPN security and peculiarities of VPN-safety, how VPN encryption guarantees the safety of your information, and why VPNs are becoming one of the inalienable tools of any internet user in the world.
________________________________________
Internet Privacy: Knowledge of Potential risks.
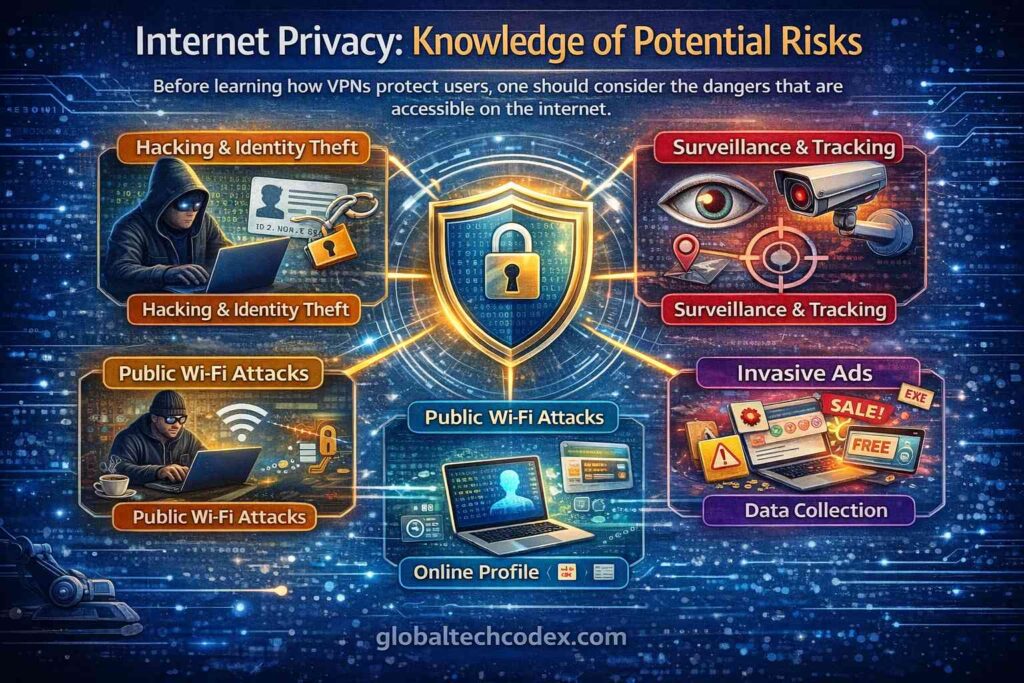
Before learning how VPNs protect users, one should consider the dangers that are accessible on the internet.
Whenever you access the internet, your device communicates with the internet sites and server. The process exposes several information such as your IP, whereabouts, history and even some personal information.
Some of the current risks of the internet include:
Data Tracking
One can find many web sites and advertisement companies, which track the user navigation. They monitor the data about the websites you visit, what you are searching or what you are watching.
ISP Monitoring
Your Internet Service Provider (ISP) can spy on you to see what you are doing on the Internet unless you post your information in encrypted ways. Browsing logs can be preserved in the ISPs in other regions.
Public Wi-Fi Attacks
Free Wi-Fi network is convenient and unreliable simultaneously. Hackers can intercept sent information by use of such networks.
Geo Restrictions
Some of the internet based services are geographically restricted.
These issues are indicative of the growing need of a more efficient privacy tool, and VPN technology can fix a significant number of such problems.
________________________________________
How VPN Secure Data Encryption.
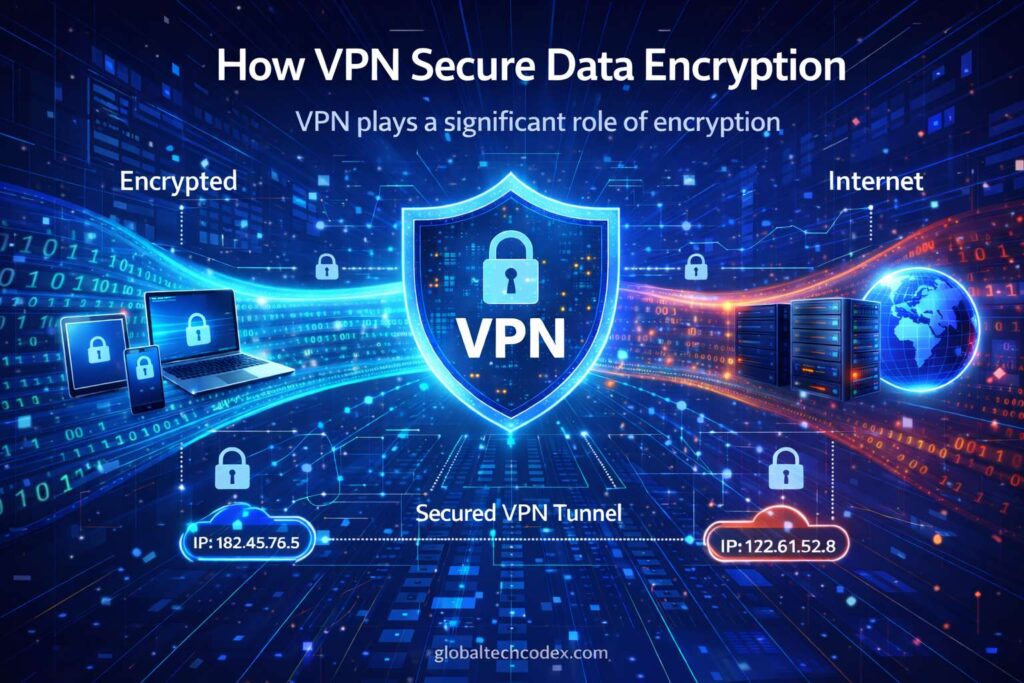
VPN plays a significant role of encryption.
Encryption codes your information to a form that is not understandable and then it passes the internet. The target server was the only server that could decrypt this information and understand it.
Unless you are using encryption, you are liable to being hacked or at worst, third parties may follow your trafficking across the internet.
The process to follow when utilizing a VPN is usually the following:
1. You initiate the VPN application in your machine.
2. The VPN creates a safe connection with one of its hosts.
3. Encryption of your data will take place before it leaves your machine.
4. The coded message is transmitted in an unassailable corridor.
5. The vpn server decrypts it and transmits them to the web site.
6. With the help of the site, the response is sent in the same secure tunnel.
With this process of encryption, a third party whose interest is to intercept your internet traffic will only get a scrambled information.
This makes the VPNs to be of value all the more when an individual is using sensitive information such as the bank websites, email accounts or even online payment systems.
________________________________________
Security Characteristics of VPN.
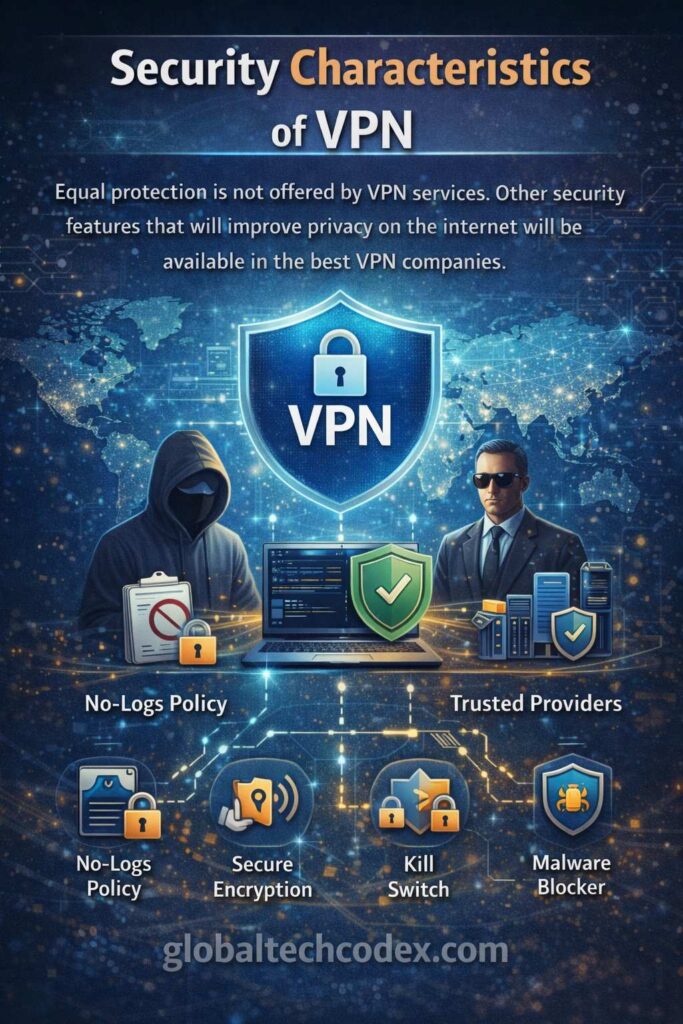
Equal protection is not offered by VPN services. Other security features that will improve privacy on the internet will be available in the best VPN companies.
Some of the key features of a secure VPN include the following.
Efficient Encryption Standards.
Most of the reputable VPN providers depend on the AES-256 encryption that is also considered as one of the strongest encryption systems available. Governments, financial institutions and other security organizations regularly employ the encryption standard.
No-Logs Policy
A trustworthy VPN firm should follow the strict no-logs policy. It means that the provider will not record your browsing history or connection logs or IP addresses.
And this is what ensures that the online presence of any company is not traceable by VPN.
Kill Switch Protection
A kill switch is one of the safety measures. A kill switch will prevent the traffic to the internet in case your VPN connection goes dead.
DNS Leak Protection
The devices will sometimes issue accidental requests outside the tunnel of VPN, and you will be unveiled. DNS leak defense prevents this issue by ensuring that all the traffic is directed to the VPN server.
Multiple Server Locations
The companies that offer VPN services are typically located in two or more nations. This will allow interrelating with the users in other areas and enjoy privacy.
A higher rate of connection and stability can be also provided through an increased number of server options.
________________________________________
Common Uses of VPNs
VPNs have a wide set of applications. Even though the main reason behind their utilization is that of privacy, they do have other practical applications, which they advocate.
Securing Personal Privacy.
VPNs are also applied to prevent the monitoring of location and Internet habits of the websites and the advertisers using your IP address.
Safer Public Wi-Fi Browsing
Using the public Wi-Fi networks is frequently targeted by the hackers. The information is secured by VPN encryption when utilizing such networks.
Secure Remote Work
The VPNs are also being used to give employees a chance to use the company networks in a safe manner when they are out of work and at home.
Secure File Sharing
VPNs will act as an additional protection of privacy in the sharing of files over the internet.
Accessing Global Content
Others also use VPN to access websites or stream sites which it may be limited in location.
________________________________________
VPNs Legal?
In most of the states, VPNs are not illegal and it is not only companies but individuals who use them.
VPN technology can help most companies possessing sensitive information to have remote access to internal system.
Nevertheless, the usage of VPN is being limited or controlled by some of them as per the government policy with regards to the use of internet and censorship.
It is advisable that a user should always make sure that he or she reads, the local laws and regulations on the use of VPN in the area.
________________________________________
Prison Break What is the difference between VPN and Proxy?
VPNs and proxy servers are not analogous to each other, as they are confused by other people.
Use of the proxy server conceals your IP because it is used in another server to redirect traffic. Your data are not however normally encrypted with the proxies.
A VPN will however go beyond masking your IP address but it will also encrypt your traffic. This renders VPNs highly secure as compared to proxies.
The usage of VPNs is typically advisable to users, due to this, they would desire to be discreet and secure.
________________________________________
How to Choose the Right VPN
The list of VPN providers is very high, and there is the issue of choosing the appropriate one. These are just the key issues that one should consider when deciding on VPN service.
Security Features
Find a great encryption, and DNS protection, and kill switch.
Privacy Policy
Select a provider that has open no-logs.
Server Network
It would possess better locations of the server to offer optimal performance and flexibility.
Speed and Performance
Good VPNs optimize servers in such a way that they make use of the slowdown speed.
Device Compatibility
Make sure that VPN is compatible with Windows, Android, iOS, macOS and routers.
Customer Support
Good VPN has good customer services and they have easy-to-follow instructions in terms of installing their products.
________________________________________
The Future of VPN Technology
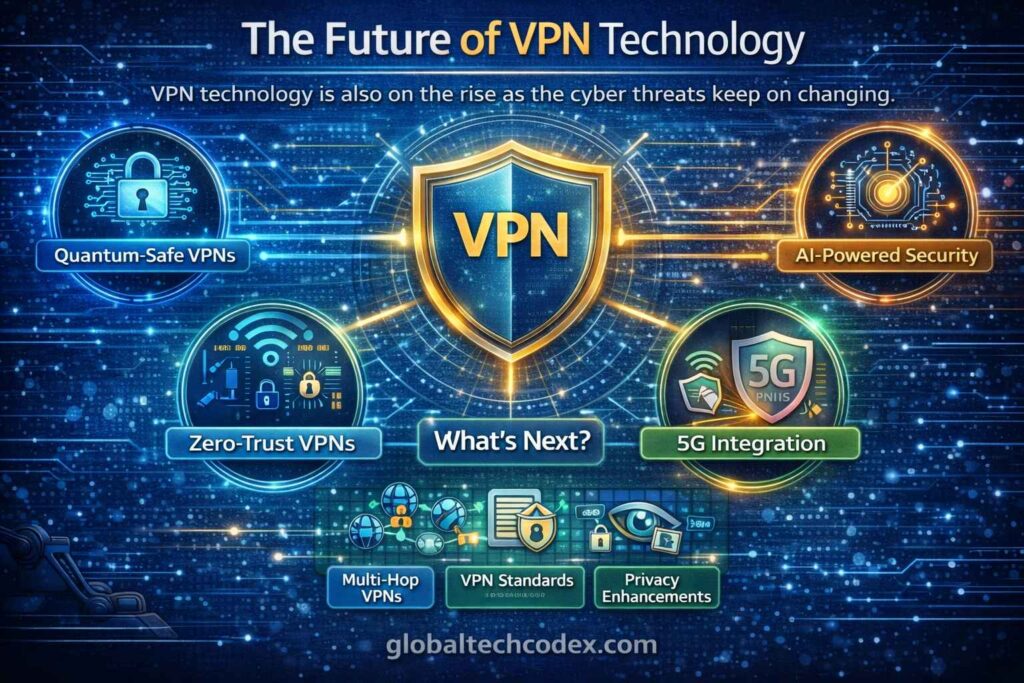
The VPN technology is also on the rise as the cyber threats keep on changing. Developers of the same are in a consecutive fight to enhance encryption, connection speed and privacy.
The improvements of VPN service technologies are proposed in the forms of WireGuard protocols, enhanced server infrastructure, and enhanced privacy policy so that it could become faster and safer.
Meanwhile, it is true that Internet privacy is becoming a popular consciousness. Increasing numbers of users understand the need to ensure that personal information remains safe and has the right to control what they do online.
Due to this fact, it is also likely that the VPN use would keep growing in the nearest future.
________________________________________
Conclusion
The possibilities offered by the internet are fantastic and so is the privacy and security threats. Therefore, now than ever before, there is a need to protect your personal information.
One of the best alternatives that may be embraced to enhance privacy on the net, and to protect the internet connections, is the Virtual Private Network. VPN will also assist in preventing hackers, spies and any other undesirable surveillance since it codes the information and hides the IP address.
VPNs cannot completely remove all the cybersecurity issues, but they make a great contribution to the fact that individuals have a safer internet experience.
With safe VPN and good browsing behavior, good passwords and advanced security programs, you will be much more secure in the internet.
With the ever-increasing popularity of the digital world, it is probable that such technology, as VPNs, will remain in the arsenal of every person who values his/her or her privacy, safety, and liberty in the digital world.