The present digital arena is changing at a very fast pace in relation to cyber security threats. One of the examples of the threats that are constantly facing organizations is data breaches, ransomware attacks etc. thus, the ethical hacking is one of the methods that can be used to ensure that systems and networks are safe and information is highly secured.
Therefore, in this beginner friendly tutorial, when you are interested in the field of cybersecurity and wish to understand how the mechanics of ethical hacking, you will be equipped with the groundwork, equipment, skill and the future careers in the field of ethical hacking.
________________________________________
What Is Ethical Hacking?
Ethical hacking or a legal hacking is a hacking of computer systems, networks and applications with a view of identifying their vulnerabilities before the malicious hackers get a chance to exploit the vulnerabilities. White hats hackers can also be called ethical hackers.
The ethical hackers do it with permission and within the law unlike the cybercriminals. They are aimed at making sure that security is increased and the problems and recommendations are provided.
Types of Hackers
White Hat Hackers- Lawful hackers in the process of testing the systems.
Black Hat Hackers – The hackers who exploit the loopholes to get themselves wealthy.
Gray Hat Hackers- They act somewhere in a grey space between ethical and unethical sometimes, unauthorized, and with no ill intent.
White hat hacking is not accessible to legitimate and legal practices.
________________________________________
The Justification of White Hat Hacking.
Attacks on computers may lead to loss of money, reputation and interruption of operations.
• Identify areas of weaknesses in front of the attackers.
• Strengthen system defenses
• Meet cybersecurity laws.
• Protect customer data
• Build trust with users
The digital transformation is continuously rising, and the moral hackers are being in demand in the financial, healthcare, government, and technology segments among others.
________________________________________
Key Concepts You Should Know
It has its simple notions of cybersecurity that one should learn before moving on to tools and techniques.
1. Vulnerability
A system can have a weak point that is exploited by an attacker.
2. Threat
It is one of the possible weaknesses that can be applied.
3. Exploit
An approach or an instrument of exploiting a weakness.
4. Penetration Testing
The system security is tested by proposing and simulating cyberattacks.
5. Social Engineering
Leaking classified information out of people.
These are the fundamentals that would assist you in developing the ethical hacking base.
________________________________________
Types of Ethical Hacking

Ethical hacking may be divided into a number of spheres:
Network Hacking
Web Application Hacking
Determining vulnerabilities of web applications and web sites e.g. SQL injection and cross-scripting.
System Hacking
Bugs in privilege escalation, or bugs in proofreading code operating systems on the wrong settings.
Wireless Network Hacking
Checking the vulnerability of Wi-Fi vulnerability in security and encryption.
Mobile Application Hacking
Determining the weaknesses of Android and iOS apps.
The region needs to have many tools and skills.
________________________________________
Skills at the beginner level were necessary.
To hack ethically, there is the need to have technical and analytical intelligence. The most significant ones are the following:
1. Networking Knowledge
Knowledge of TCP/IP, DNS, HTTP and firewalls.
2. Operating Systems
Master Linux, particularly, Linux security based such as Kali Linux.
3. Programming Skills
Python, Bash scripting, and JavaScript As a low-level skill, it is very convenient.
4. Familiarization with Security Protocols.
Get familiarized with encryption, authentication, and encryption systems, and SSL/TLS.
5. Problem-Solving Skills
Ethical hackers have to be imaginative and logical.
________________________________________
The most General Ethical Hacking Tools.
An appropriately acting hacker is able to test and secure systems with special tools. The following are some of the common tools:
1. Nmap
Applied in port scanning networks, and in port location.
2. Wireshark
Scans traffic over the network and identifies suspect traffic.
3. Metasploit
An effective testing model of vulnerability.
4. Burp Suite
It is used to test the security of the web applications.
5. John the Ripper
Verifications of the password strength and security.
They should not be used in such locations where they are not permitted like the laboratories or unauthorised.
________________________________________
The Ethical Hacking Process
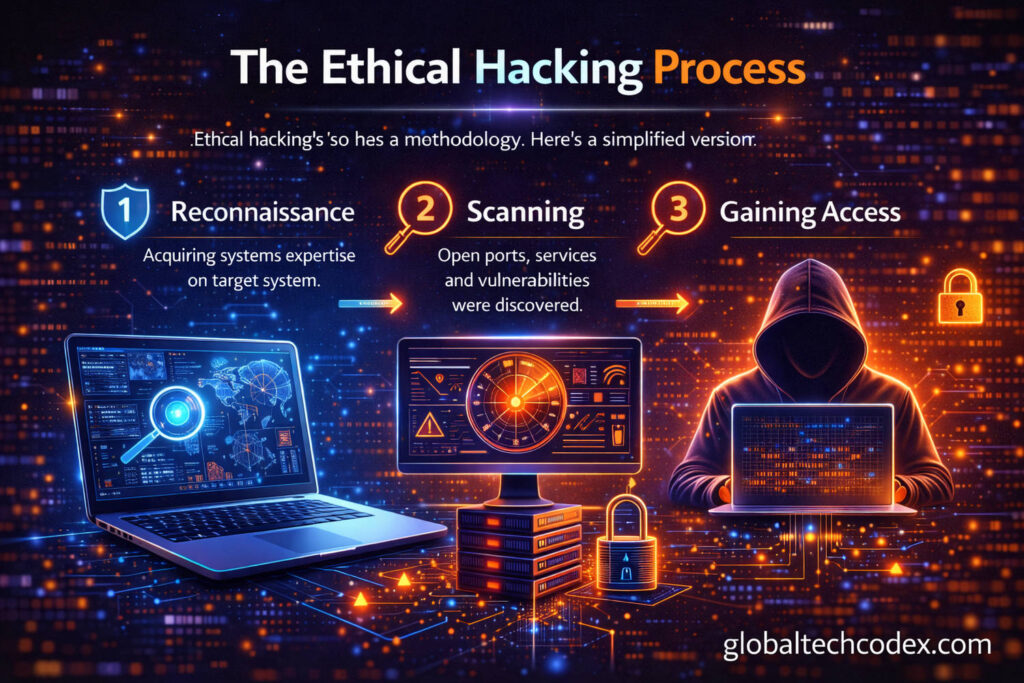
Ethical hacking has a methodology. Here’s a simplified version:
1. Reconnaissance
Acquiring systems expertise on target system.
2. Scanning
Open ports, services and vulnerabilities were discovered.
3. Gaining Access
Trying to work on the weak points in a kind of a manipulating way.
4. Maintenance (Simulation Only) Access.
Resilience methods used to test system resilience.
5. Reporting
Writing down vulnerabilities and security recommendations.
Reporting is among the steps that are most important. Hackers who are ethical are expected to report dangers and solutions to companies.
________________________________________
Legal and Ethical Concerns.
The legal provisions on the ethical hacking should be very strict. In order to test any system you need:
• Written authorization
• A defined scope of testing
• Clear documentation
Another type of crime that is punishable by the law even though one may not do it with bad intentions is illegal hacking.
When reporting the vulnerabilities, responsible disclosure must be observed at all times.
Introduction-level Certifications.
In case you are keen on becoming an ethical hacker as a career, then the credibility that you possess can be enhanced with the help of the use of certifications.
EC-Council
Certifies the Certified Ethical Hacker (CEH) certification.
Offensive Security
Offers the certification of the OSCP (Offensive Security Certified Professional).
CompTIA
Certify beginners as Security +.
There are certifications which are applied to certify your skills and increase the opportunities of getting employed.
________________________________________
How to Start as a Beginner
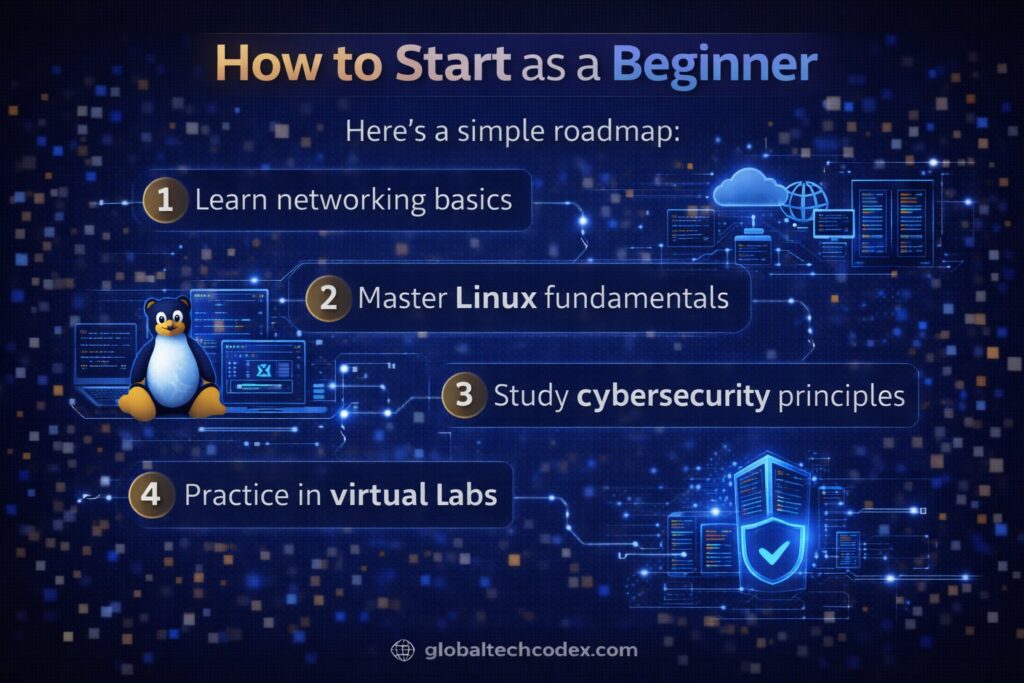
Here’s a simple roadmap:
1. Learn networking basics
2. Master Linux fundamentals
3. A review of literature regarding the concept of cybersecurity.
4. Practice in virtual labs
5. Attend Capture The Flag (CTF).
6. Create a house laboratory with VM.
7. Keep learning and drilling.
The platforms involve some of the online cybersecurity lab and simulation environment that enable beginners to train on a safe platform.
________________________________________
Career in Hacking Ethics.
The White hat hacking presents an opportunity to most jobs:
• Penetration Tester
• Security Analyst
• Red Team Specialist
• Cybersecurity Consultant
• Security Engineer
As a result of the increased number of cyber threats, the number of qualified ethical hackers is also increased in the world.
________________________________________
Knowledge on Hacking Ethically.
Ethical hacking may be an intensive one, yet it is a hurry:
• Constant learning required
• High responsibility
• Rapidly evolving threats
• Legal accountability
Nevertheless, it is a very satisfying profession to the individuals who are consumed with cybersecurity.
________________________________________
Conclusion
Hacking ethically is not about destroying the systems but ensuring that they are secure. It has a balance of technical capabilities, creativity and accountability to prevent cyber threat.
The entry point begins with networking, operating systems, and security basics because someone can be a beginners who does not know how to make his or her way around these concepts. The profession of cybersecurity has the potential of a bright future and it could be achieved through practice, certification and ethical commitments.
Today, ethical hackers in the profession are in demand more than ever and with time and constant education, you will become one.