Complete Guide to Media Access Control Addresses
Identification of all the devices in a networked system should be through a method. Where the IP addresses aid the devices to communicate using the internet there is yet another identification in the background the MAC address.
The local networks insist on using MAC address in communication. Devices would fail to know where to send any kind of information to the hardware that is concerned. MAC address is a complicated tutorial and hence it will project the understanding of a MAC address, how it functions, its format, types, problem of security and distinction between a MAC address and an IP address.
________________________________________
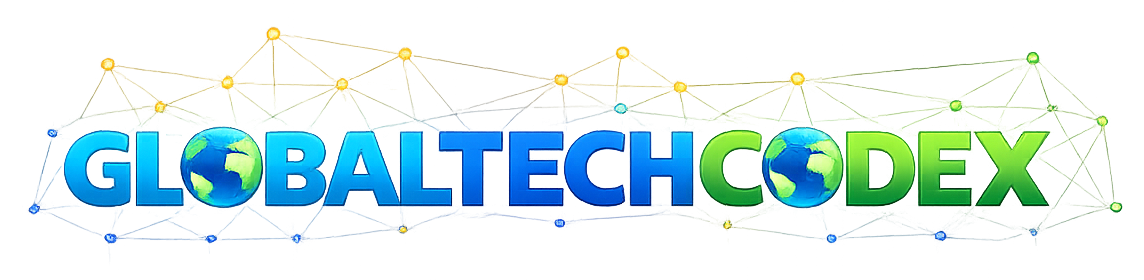
What Is a MAC Address?
MAC (Media access Control) address Special hardware address and is assigned to a network interface device in the network. It allows the machines within the same local network (LAN) to identify each other and communicate with one another.
The manufacturer hard writes an MAC address on the NIC of the device as compared to the dynamic IP address.
You can think of it as:
• IP address = Mailing address
MAC address = Mail box serial number.
MAC address = Mailbox number.
They are needed in one way or the other.
________________________________________
What Does MAC Stand For?
MAC is an abbreviation of Media access control that is the sub-layer of Data link layer of OSI (ostensible systems integration) model.
OSI model isolates the network communication into seven layers. The MAC address operates at:
Layer 2 – Data Link Layer
This means, that it links MAC addresses within the same part of the network and not the whole internet.
________________________________________
Structure of a MAC Address
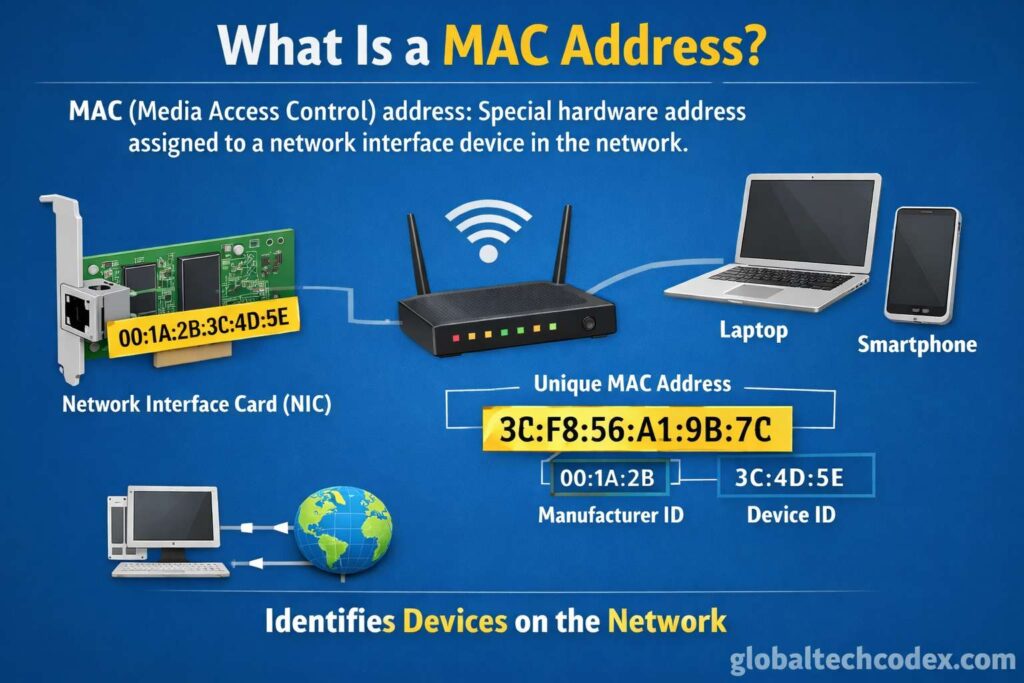
A traditional MAC address is:
• 48 bits long
• In hexadecimal notation.
Grouped in 6 blocks of 2 hexadecimal characterizations.
Example:
00:1A:2B:3C:4D:5E
Breakdown of a MAC Address
MAC address consists of two large components:
1. Organizational Unique Identifier (OUI).
The manufacturer of it is calculated by using the first 24 bits (first three octets).
These OUIs are allocated under the Institute of electrical and electronics engineer.
2. Device Identifier
The 24bits that are left are specific to the device.
This ensures that no two similar gadgets will have identical MAC address of the same producer.
________________________________________
Types of MAC Addresses
The MAC addresses differ on many terms in regard to their assignment and application.
1. universally administered address (UAA).
• Assigned by manufacturer
• Globally unique
• Most common type
2. Locally Administered Address (LAA).
• Manually assigned
Utilized when in special set-up or virtualization.
• Manufacture delegates squashes out.
3. Unicast MAC Address
Used to find a single device.
4. Multicast MAC Address
The message was sent to communicate to a set of devices.
5. Broadcast MAC Address
The special address:
FF:FF:FF:FF:FF:FF
This transmits data to the rest of the devices of a local network.
________________________________________
MAC Addresses Network working.
ARP (ARP protocol) transports utilization of MAC addresses in the physical networks.
Here’s how it works:
1. It takes some information that has to be sent into a machine.
2. It knows the IP address and not theMAC address.
3. It sends ARP request on the network.
4. The IP machine responding will respond with a MAC address.
5. Communication begins.
This is made possible so as to transform IP-based communication to delivery on hardware level.
The routers that use them are able to communicate with IP addresses over the networks, yet MAC addresses.
MAC Address vs IP Address
Understanding the difference is critical.
| Feature | MAC Address | IP Address |
| Layer | Data Link (Layer 2) | Network (Layer 3) |
| Assigned By | Manufacturer | ISP or Network Admin |
| Permanence | Usually permanent | Often changes |
| Format | 12 hex digits | Decimal or hex |
| Scope | Local network | Global internet |
MAC addresses are being used in local delivery and the IP addresses being used whenever routing between networks.
________________________________________
Where MAC Addresses Are Used
The network is mostly used in applications that need MAC addresses:
1. Intranet Communication.
MAC addresses redirect the data to the relevant device using switches.
2. MAC Filtering
The routers are able to block the access to the networks according to the MAC addresses.
3. Device Identification
MAC address is used to identify the devices by the network administrators.
4. DHCP Reservations
A fixed IP address will be allocated to a given device with a predetermined fixed IP address depending on its MAC address.
5. Wi-Fi Authentication
The accepted MAC addresses are only those included in some networks.
________________________________________
MAC Address and Network Switches.
AMAC address table is being stored in switches.
When data arrives:
1. MAC address of the source is detected by the switch.
2. It captures the port to which the MAC address is attached to.
3. It only pushes information into the destination MAC port.
This renders it easy to switch and also saves time and unwarranted traffic.
________________________________________
MAC Address Randomization
Randomization of MAC addresses now is supported by the modern devices.
Why?
Privacy concerns.
In case you are connected to communal Wi-Fi then your device advertises its MAC address. When businesses were across networks, cloud-tracing of the devices was available.
The Mac addresses are randomized to lower tracking through scanning of the operating systems.
Privacy is guaranteed by randomization but it is difficult to regulate the network.
________________________________________
MAC address based security threats.
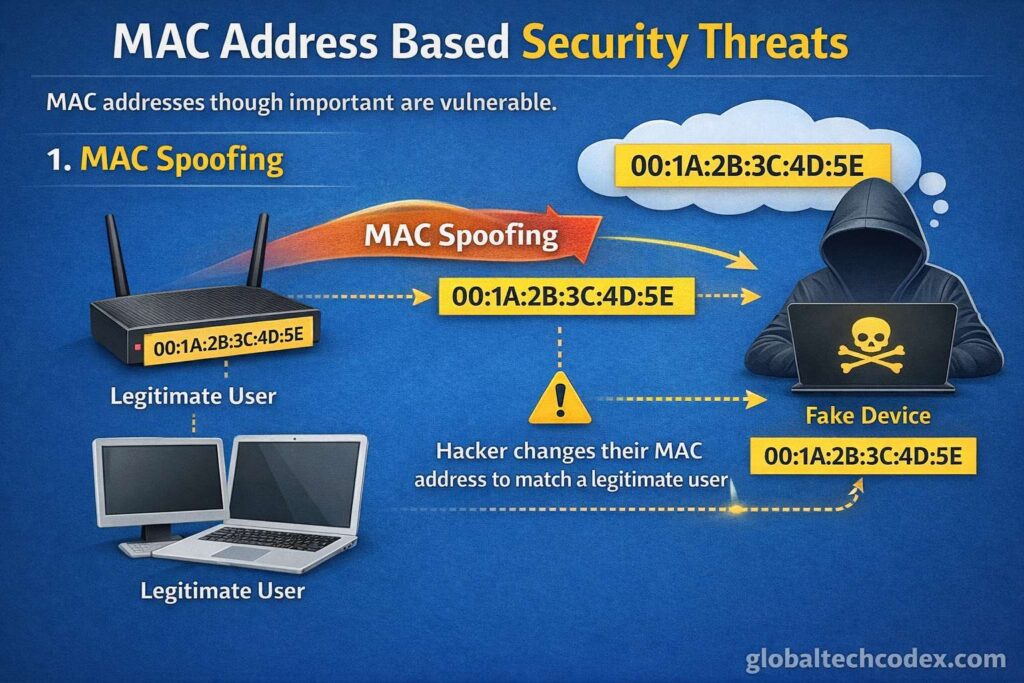
MAC addresses though important are vulnerable.
1. MAC Spoofing
The attackers have the opportunity to modify theMAC address of their device to impersonate another device.
This is called MAC spoofing.
Used for:
• Bypassing MAC filtering
• Network impersonation
• Testing security systems
2. MAC Flooding Attack
A hacker inundates a switch with fabricated MAC-address.
This causes:
• MAC table overflow
• Switch acting like a hub
Both of them are very susceptible to packet sniffing.
3. Tracking Concerns
Wi-Fi probes had also been employed by retail stores to monitor the movement of customers using MAC address.
Some firms have either eliminated or anonymized the practice because of the privacy laws.
________________________________________
How to Find Your MAC Address
On Windows
ipconfig /all
On macOS
ifconfig
On Linux
ip link show
On Smartphones
Settings-> about phone- status- wifi MAC address.
________________________________________
Is a MAC Address Truly Unique?
In theory, yes.
In practice:
Manufacturers are capable of doing the wrong thing.
It is possible to copy addresses in the virtual machine.
• Users can spoof addresses
Nevertheless, in practice collisions are virtually impossible.
________________________________________
MAC Addresses of Virtue and Cloud computing.
MAC addresses are also virtual machines (VMs).
Platforms such as:
• VMware
• VirtualBox
create virtual MAC addresses of virtual network interfaces.
MAC addresses of the virtual network adapters are dynamically allocated by cloud providers.
________________________________________
MAC Address in IoT Devices
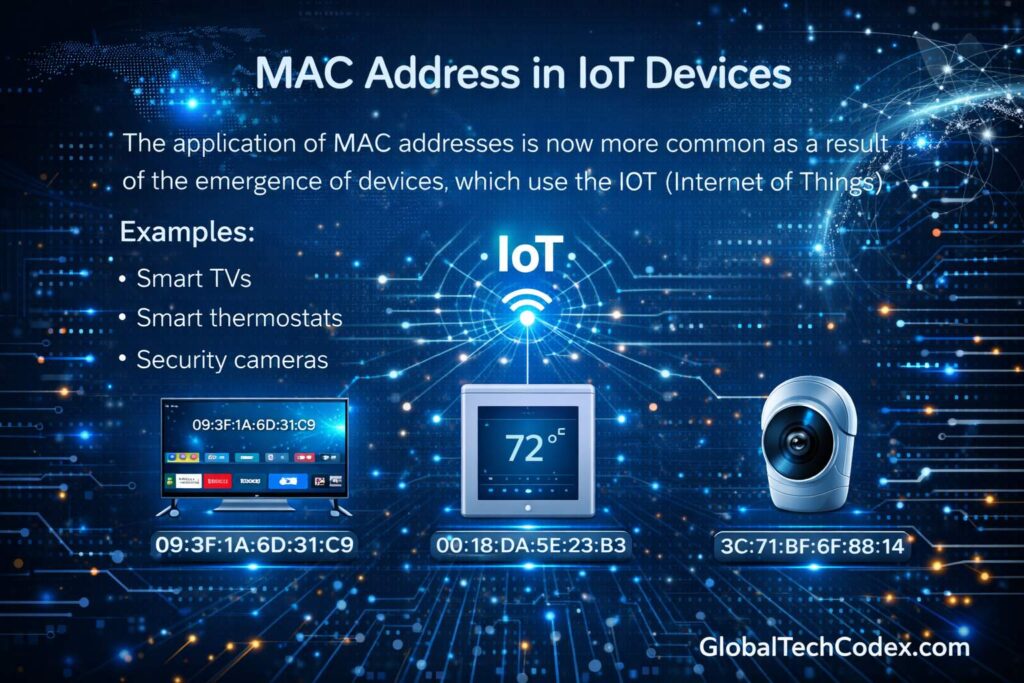
The application of MAC addresses is now more common as a result of the emergence of devices, which use the IoT (Internet of Things).
Examples:
• Smart TVs
• Smart thermostats
• Security cameras
• Smart speakers
MAC address is a local network communication address, which is implanted in each device.
It is what renders the security of MAC-level even more crucial.
________________________________________
Can a MAC Address Be Changed?
Yes -but in the short run in most instances.
The process is referred to as MAC spoofing.
if possible changing MAC address:
• Privacy protection
• Network testing
• Bypassing MAC filtering
This can however breach the network policies in caseMAC addresses are modified without permission.
________________________________________
Legal and Privacy Filming.
MAC addresses can be regarded as personal information including:
General Data Protection Regulation.
Organizations must:
data gathering Notice users.
• Secure stored network logs
• No unjustified retention.
The aspect of privacy compliance is becoming a concern in the enterprise networks.
________________________________________
Future of MAC Addressing
With network expansion and transformation, the Ethernet communication still relies on MAC addresses.
However, trends include:
• Increased randomization
• Stronger encryption
Software-defined networking A network system, also known as software-defined networking (SDN), is a network system that can be described as software, rather than hardware.
• Zero-trust network models
Despite these developments, the MAC addresses remain a simple part of the local communication of the devices.
________________________________________
Frequently Asked Questions
Is somebody hacking me with my MAC address?
Not in a face-to-face manner. The MAC addresses are not transmitted in local networks.
Does VPN hide my MAC address?
No. VPNs never conceal your MAC address, but the IP one.
Is MAC filtering secure?
Not very. MAC spoofing can be used in bypassing it.
all devices are have MAC addresses?
Yes, it can support any device, which can be connected to the network (Ethernet, Wi-Fi, Bluetooth).
________________________________________
Conclusion
One of the easiest components of networking is a MAC address. It allows domestic communication, network administrators can use networks to control the switching of traffic using switches and devices.
Whereas the IP addresses are preoccupied with routing on the global front, the MAC addresses provide the data with the specific hardware on an area network.
The MAC addresses have never been more critically important to learn than they are today due to the increasing popularity of the IoT and virtualization, as well as the awareness of privacy. You might be a layman in the fundamentals of network or a highly skilled IT professional who is dealing with the infrastructures of a large organization but, having the knowledge of the concepts of MAC address will help you realize how networks work internally.