We live in the world today as a global village where practically everything that we do is associated with the internet be it banking, shopping, work and communication. This connectivity also puts both the devices and the networks at the risk of cyber attacks even though this connectivity is convenient. Every region of the world has the occurrence of malware, computer intruders, and ill will to compromise the system once in every second. At this point, firewall appears to be one of the most requested in relation to cybersecurity.
Firewall is a security barricade of the internet, between your internal and external network which might not be as reliable as the internet. Granted that it is a virtual guard, which examines and blocks the traffic around the entrance and exit considering the security policies which have been set earlier. Your house is the house with no firewall, i.e. open door policy.
We will decipher the nature of a firewall, its application, and the different nature of firewall and its significance.
________________________________________
What Is a Firewall?

A network security technology, a hardware or software-based or a combination of hardware/software firewall, is the one which provides a filter of the network traffic or network exit. It affixes that which shall pass and that which shall be hindered.
The primary activity of firewall is the following:
In order to avoid the unauthorized access and, simultaneously, allow the legitimate communication.
Firewalls have rules, which guide the behavior of data packets either by allowing them or by blocking them. Such rules are founded on IP addresses, domain names, protocols, ports and application behaviour.
Firewall is nothing more than a checkpoint at the border. All the data should indicate their credentials before they are in or out of the system.
________________________________________
Why Firewalls Are Important

The cyber threats keep on changing. The systems are insecure and are subject to:
There are attackers who make an attempt to steal valuable information.
• Malware infections
• Ransomware attacks
• Spyware and data leaks
• Unauthorized remote access
• Robots and automatic attacks.
Firewall mitigates these threats by establishing a security barrier that blocks bad traffic even before it becomes malicious.
Firewalls are important for:
• Personal computers
• Smartphones
• Corporate networks
• Cloud environments
• Data centers
Intelligence of the Internet of Things (IoT) communications.
Firewall protection is also built in even the home Wi-Fi routers.
________________________________________
How a Firewall Works
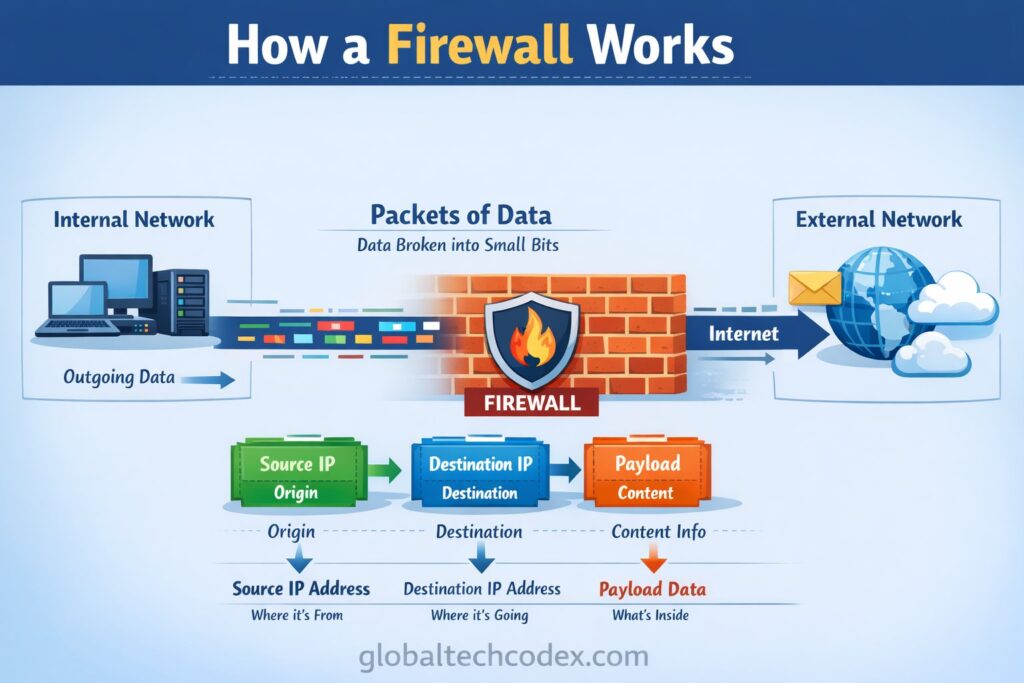
In case data is sent over the internet it is disaggregated into small bits referred to as packets. The packets include information on the origin, destination and contents.
A firewall analyses these packets and they are processed according to the security rules. The firewall will under such regulations:
• Allow the packet
• Block the packet
• Log the activity for review
• Alert administrators
The firewall may handle the traffic in various ways depending on its complexity. The authenticated source and destinations address can be performed using simple firewalls and application level activity and suspicious behavior may be detected using the advanced firewalls.
Other firewalls also make records of the connections which are alive and only the legitimate sessions are stored.
________________________________________
Types of Firewalls
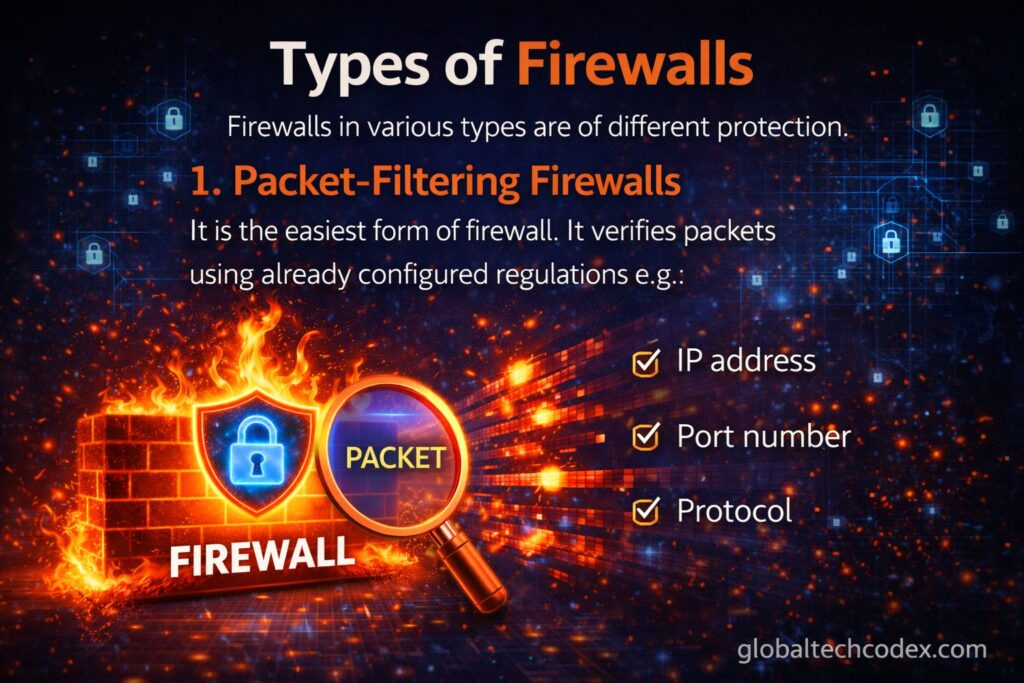
Firewalls in various types are of different protection.
1. Packet-Filtering Firewalls
It is the easiest form of firewall. It verifies packets using already configured regulations e.g.:
• IP address
• Port number
• Protocol
In a situation where the confirmation of a packet is done with a packet that has been allowed it is passed on. Otherwise, it is blocked.
Advantages:
• Fast and efficient
• Simple to implement
Disadvantages:
• Limited intelligence
• Cannot inspect data deeply
________________________________________
2. Stateful Intrusion Firewalls.
Firewalls remember, and can know what is going on in the network traffic. They are not viewing packets but viewing sessions.
This renders them more resilient unlike the simple packet filters since they are able to detect suspicious traffic on an active connection.
Advantages:
• Stake on increased security as compared to packet filtering.
• Knows traffic environment.
Disadvantages:
• Slightly slower
• Consumes greater resources of the system.
________________________________________
3. Proxy Firewalls (Application-Level).
A proxy firewall is a firewall that isolates the user and the internet. Direct and proxy server are used in transferring.
The proxy caches the traffic across the application layer and has the capability to block content of choice.
Advantages:
• High level of security
• Inclusiveness internal network architecture.
Disadvantages:
• Slower performance
The installation of the may need is complex.
________________________________________
4. Next-Generation Firewalls (NGFW).
The new generation firewalls possess the rudimentary firewall capabilities but enhanced capability such as:
• Deep packet inspection
• Intrusion prevent system (IPS).
• Application awareness
• Malware detection
• User identity tracking
Such firewalls will fight the contemporary cyber attacks and are common within the business environment.
Advantages:
• Advanced protection
• Full security facilities.
Disadvantages:
• Higher cost
• Needs a well educated management.
________________________________________
5. Hardware Firewalls Software vs Hardware Firewalls.
Hardware Firewalls
• Placed as physical devices.
• Protect entire networks
• Businesses and routers.
Software Firewalls
Embarked on personal computers.
• Protect single computers
Many of them are embedded into operating systems.
The two are used layered by many of the organizations.
Benefits of Using a Firewall
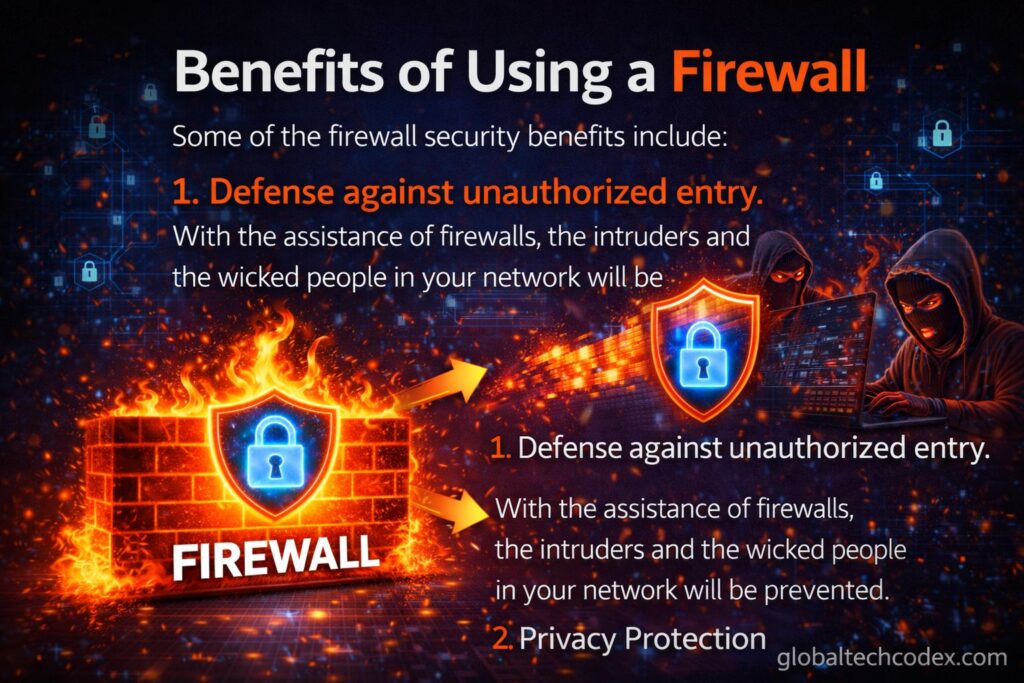
Some of the firewall security benefits include:
1. Defense against unauthorized entry.
With the assistance of firewalls, the intruders and the wicked people in your network will be prevented.
2. Privacy Protection
The absence of this confidential information is not experienced because of the dispossession of unofficial data transfer.
3. Network Monitoring
The traffic information is also stored in the firewalls and this assists the administrators to scrutinize the suspicious activity.
4. Access Control
It is also able to limit the usage or the access of applications or sites by the staff in an organization.
________________________________________
Limitations of Firewalls
That should not be foolproof firewalls they should have.
They are not put in this position to prevent the attacks that can be experienced in the network.
• They can be phishing or social engineering ignorant.
Security holes may occur as a result of misconfiguration.
No substitute of user awareness or antivirus.
Firewalls may be outlined within an extensive cybersecurity plan present.
________________________________________
The existing Firewalls and Cybersecurity.
The hack threats that exist are more sophisticated. The sophisticated techniques are the utilization of encrypted malware, zero days and artificial intelligence attack.
Along with deployment of innovative firewalls is:
• Cloud security systems
• Threat intelligence feeds
• Behavioral analytics
• Endpoint protection
• AI-based detection tools
They do not filter platforms even more but intelligent security platforms.
Firewalls have also been enhanced as a result of the spread of remote work and cloud computing to maintain the security of the distributed network and the virtual environment.
________________________________________
Best Practice of firewall using.

In order to make firewalls the most efficient:
Use effective rule settings.
• Disable unused ports
• Monitor logs regularly
The antivirus programs: Work with them together.
• Cyber risks: Educate users.
Multi-level security will be taken.
Among security there are some that are more accommodative in as far as defensive is concerned.
________________________________________
Conclusion
One of the most demanded items of the digital security world is a firewall. It forms a barricade between a trusted system and the threats that might occur, it creates traffic controls along with it prevents unauthorized access. Firewalls are an important aspect of the contemporary day cyber security of large and small enterprises.
A firewall is not sufficient though. It will be installed with a relevant security feature, software modifications, and training to customers. Cybersecurity is not a tool but the process that is one-dimensional.
There is the changing technology and cyber threats will change. The firewalls will not be involved in the defense process, but will conform to the arising issues, and first of all the safety of the digital world, which we are so reliant on in the day to day basis.